The Complete VAPT Methodology: Step-by-Step Walkthrough
Cyberattacks in 2026 are no longer opportunistic they are engineered. Ransomware-as-a-Service groups, nation-state threat actors, and AI-assisted exploits have made the question not if your organization will be targeted, but when. At the same time, regulatory bodies are tightening their grip: SOC 2, ISO 27001, PCI-DSS, and HIPAA all increasingly require evidence of structured security testing, not just perimeter firewalls and antivirus licenses.
This is precisely why Vulnerability Assessment and Penetration Testing (VAPT) has become one of the most critical security investments for CISOs, IT security teams, SaaS startups, fintech companies, and enterprises alike. A one-time automated scan tells you where holes might exist. A complete VAPT methodology tells you exactly how an attacker would exploit them and what to do before they get the chance.
This guide walks you through the complete VAPT methodology step by step, covering every phase from initial scoping to final remediation along with tools, testing types, common pitfalls, and how to choose the right VAPT service provider for your organization.
VAPT (Vulnerability Assessment and Penetration Testing) is a structured security testing process that combines automated vulnerability scanning with manual exploitation techniques to identify, validate, and prioritize security weaknesses across an organization’s digital infrastructure before attackers do.
What Is VAPT and How Does It Work?
VAPT combines two distinct but complementary disciplines. A Vulnerability Assessment (VA) systematically identifies and classifies known security weaknesses using automated tools and manual inspection. A Penetration Test (PT) goes further: a skilled security professional actively attempts to exploit those weaknesses to determine real-world impact.
Together, VAPT provides:
- Scope: Breadth of coverage across systems, applications, and networks
- Depth: Manual exploitation of discovered vulnerabilities to confirm severity
- Context: Business-risk-aligned reporting, not just a list of CVE scores
- Compliance evidence: Documented proof for SOC 2, ISO 27001, PCI-DSS, and HIPAA auditors
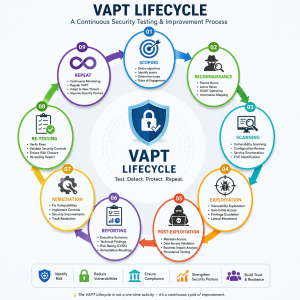
The Complete VAPT Methodology: Step-by-Step Process
A professional VAPT engagement follows a rigorous, repeatable process. Here are the seven core phases of the complete VAPT methodology:
01 Scoping & Rules of Engagement
Define the systems in scope (IPs, domains, applications), testing windows, and legal authorization. A formal Statement of Work (SoW) and authorization letter are signed before any testing begins. This step prevents scope creep and ensures legal compliance.
02 Reconnaissance (Information Gathering)
Testers collect publicly available information about the target: subdomains, open ports, employee data (OSINT), technology stacks, DNS records, and more. Passive reconnaissance avoids touching target systems; active reconnaissance involves direct interaction. Tools: Shodan, Maltego, OSINT Framework, theHarvester.
03 Vulnerability Scanning & Enumeration
Automated scanners map the attack surface, identify open services, outdated software, misconfigurations, and known CVEs. Results are then manually triaged to remove false positives. Tools: Nessus, OpenVAS, Nmap, Nikto.
04 Exploitation (Active Penetration Testing)
Ethical hackers attempt to exploit confirmed vulnerabilities to determine real-world impact — escalating privileges, accessing sensitive data, or moving laterally within the network. This is what separates VAPT from a basic scan. Tools: Metasploit, Burp Suite, SQLMap, Cobalt Strike.
05 Post-Exploitation & Lateral Movement Analysis
Testers simulate what a real attacker would do after initial access — privilege escalation, data exfiltration simulation, persistence mechanisms, and pivoting to other systems. This phase reveals the true blast radius of a breach.
06 Reporting & Risk Prioritization
A professional VAPT report includes an executive summary (for leadership), a technical report (for developers), and a risk-ranked findings table using CVSS scoring (Critical / High / Medium / Low / Informational). Each finding includes evidence, business impact, and a specific remediation recommendation.
07 Remediation Support & Re-Testing
The engagement isn’t over at the report. A quality VAPT provider supports your team through remediation and conducts a free re-test to verify all critical and high findings have been resolved before issuing a final attestation letter.
Types of VAPT Engagements
Not all VAPT engagements are created equal. The right testing approach depends on your threat model, compliance requirements, and what you’re trying to protect:
| Testing Type | Tester Knowledge | Best For | Simulates |
|---|---|---|---|
| Black Box | No prior knowledge of systems | External attacker simulation | Real-world external attack |
| White Box | Full access: code, architecture, credentials | Deep code-level security review | Insider threat or auditor |
| Grey Box | Partial knowledge (e.g., user-level access) | Most realistic for enterprises | Compromised employee / partner |
| Internal VAPT | Conducted from inside the network | Lateral movement risk assessment | Post-breach attacker behavior |
| External VAPT | Conducted from outside the perimeter | Internet-facing assets | Remote attacker/hacker |
| Web App VAPT | Application-focused (OWASP Top 10) | SaaS, e-commerce, portals | Web application attacks |
| Network VAPT | Infrastructure-focused | On-premise and cloud networks | Network-level exploitation |
| Cloud VAPT | Cloud-native environments | AWS, Azure, GCP workloads | Cloud misconfiguration attacks |
Tools Used in VAPT Testing
Professional VAPT combines the speed of automated scanning with the precision of manual testing. Neither alone is sufficient for thorough security coverage.
Reconnaissance
- Shodan
- Maltego
- theHarvester
- Recon-ng
Scanning
- Nmap
- Nessus
- OpenVAS
- Qualys
Exploitation
- Metasploit
- Burp Suite Pro
- SQLMap
- ExploitDB
Web App
- OWASP ZAP
- Nikto
- w3af
- Acunetix
Passwords
- Hydra
- Hashcat
- John the Ripper
Reporting
- Dradis
- PlexTrac
- Faraday
- Custom templates
Understanding CVSS Risk Severity in VAPT Reports
Every vulnerability found is scored using the Common Vulnerability Scoring System (CVSS v3.1) to help teams prioritize remediation effort:
| Severity | CVSS Score | Example | Remediation SLA |
|---|---|---|---|
| Critical | 9.0 – 10.0 | Remote code execution, admin credential exposure | Immediate (24–48 hrs) |
| High | 7.0 – 8.9 | SQL injection, broken auth, privilege escalation | Within 7 days |
| Medium | 4.0 – 6.9 | XSS, CSRF, weak SSL configurations | Within 30 days |
| Low | 0.1 – 3.9 | Information disclosure, verbose error messages | Within 90 days |
| Info | 0.0 | Best practice deviations, security observations | Next release cycle |
Benefits of Following a Structured VAPT Methodology
- Compliance readiness: Satisfy auditor requirements for SOC 2 Type II, ISO 27001, PCI-DSS, and HIPAA with documented evidence of testing
- Risk-prioritized remediation: Fix what matters most first, not just what’s easiest
- Reduced breach probability: Organizations that conduct annual VAPT are 3x less likely to suffer a material breach
- Improved developer security awareness: Developers see real exploits — not just theoretical risks
- Customer and investor trust: A VAPT attestation letter is increasingly required in enterprise vendor assessments
- Cyber insurance qualification: Insurers now require proof of periodic penetration testing for coverage
Common Mistakes Organizations Make During VAPT
Avoid these pitfalls — they cost organizations time, money, and real security improvement.
- Treating VAPT as a checkbox exercise — commissioning a test only to satisfy an auditor, without actually fixing findings
- Choosing the cheapest provider — low-cost automated-only reports miss manual, logic-based vulnerabilities entirely
- Not including all assets in scope — leaving out legacy systems or APIs creates blind spots attackers will find
- Fixing findings without re-testing — remediation is only verified when a skilled tester confirms the vulnerability is closed
- Testing only once a year — threat landscapes change quarterly; annual-only testing leaves long gaps
- No executive briefing — technical reports must translate into business risk for C-suite action
VAPT vs. Automated Vulnerability Scanning: What’s the Difference?
| Factor | Automated Scanning | Full VAPT |
|---|---|---|
| Methodology | Tool-driven, passive detection | Manual + automated, active exploitation |
| False positives | High (20–40%) | Low (manually validated) |
| Business logic flaws | Cannot detect | Identified by testers |
| Chain of attack | Not demonstrated | Full attack path shown |
| Compliance value | Limited (not sufficient alone) | High — accepted by all frameworks |
| Report quality | Generic CVE list | Business-risk report with remediation steps |
| Cost | Low | Medium–High (commensurate with depth) |
How to Choose the Right VAPT Service Provider
With dozens of vendors claiming expertise, these criteria separate professional VAPT firms from box-ticking operators:
- Certified testers: Look for CEH, OSCP, CISSP, or CREST-certified professionals not just tools runners
- Manual testing commitment: Ask what percentage of the engagement is manual. Any answer below 50% is a red flag
- Sample report: Request a redacted sample. Good reports include exploitability context and developer-ready remediation guidance
- Re-testing included: Avoid providers who charge extra for re-testing critical findings
- Industry experience: Ask for references in your sector fintech, SaaS, healthcare, and e-commerce each have unique threat models
- Compliance alignment: Confirm the provider maps findings to your specific framework (SOC 2, ISO 27001, PCI-DSS)
VAPT Frequency, Maintenance & Best Practices
How Often Should You Conduct VAPT?
- Annually (minimum): Required by PCI-DSS, ISO 27001, and SOC 2
- After major changes: New application features, infrastructure changes, M&A activity
- Quarterly for high-risk environments: Financial services, healthcare, critical infrastructure
- Before product launch: Web app VAPT before going live is non-negotiable for SaaS companies
VAPT Readiness Checklist
- Asset inventory complete and up to date
- Authorization letter / scope document signed
- Stakeholders notified (IT, legal, DevOps)
- Testing environment defined (production or staging)
- Incident response team on standby during testing window
- Remediation SLAs agreed before testing begins
- Re-testing slot booked post-remediation
Frequently Asked Questions About VAPT
VAPT is an umbrella term that includes both Vulnerability Assessment (broad, systematic scanning) and Penetration Testing (targeted, manual exploitation). Penetration testing is one component of VAPT, focused specifically on actively exploiting vulnerabilities to prove real-world impact.
Typical VAPT engagements take 5–15 business days depending on scope. A focused web application VAPT may complete in 5 days, while a full-infrastructure engagement covering network, cloud, and applications can take 2–4 weeks.
ISO 27001 Annex A control A.12.6.1 requires organizations to manage technical vulnerabilities. While it doesn’t prescribe VAPT by name, penetration testing is the industry-standard method to satisfy this requirement — and most auditors expect it.
A professional VAPT provider conducts testing within agreed rules of engagement that minimize production risk. Testing can be conducted on staging environments, or during off-peak hours for production. Critical destructive tests are always pre-approved.
A professional VAPT report includes: an executive summary, methodology overview, scope and testing timeline, full findings with CVSS scores and evidence, business impact analysis, and actionable remediation steps with developer guidance. An attestation letter is issued after successful re-testing.
Conclusion
In 2026, a robust cybersecurity posture isn’t built on good intentions — it’s built on tested, validated evidence. The complete VAPT methodology gives your organization exactly that: a systematic, structured path from unknown risk to documented, risk-ranked findings with clear remediation paths.
Whether you’re a fast-growing SaaS startup preparing for your first SOC 2 audit, a fintech company navigating PCI-DSS requirements, or an enterprise CISO looking to pressure-test your defenses before an adversary does — a structured VAPT engagement is the most direct investment in real security resilience.
The question isn’t whether you need VAPT. The question is whether you want to find your vulnerabilities first — or wait for someone else to find them for you.
Ready to Test Your Defenses? Agency1987’s certified security team delivers comprehensive VAPT engagements aligned with SOC 2, ISO 27001, PCI-DSS, and HIPAA. Get a detailed report with actionable remediation — not just a list of CVEs.
